
In 2013 a hospital was accused of conducting a medical kidnapping against a young girl name Justina. This enraged many people across the country, including members of anonymous. A DDOS attack was waged against the hospital.
We need more people attacking 184.154.224.18, fire up your VPN & Tor's Hammer! #OpJustina #Anonymous #Target
— AnonMercurial (@AnonMercurial2) March 25, 2014
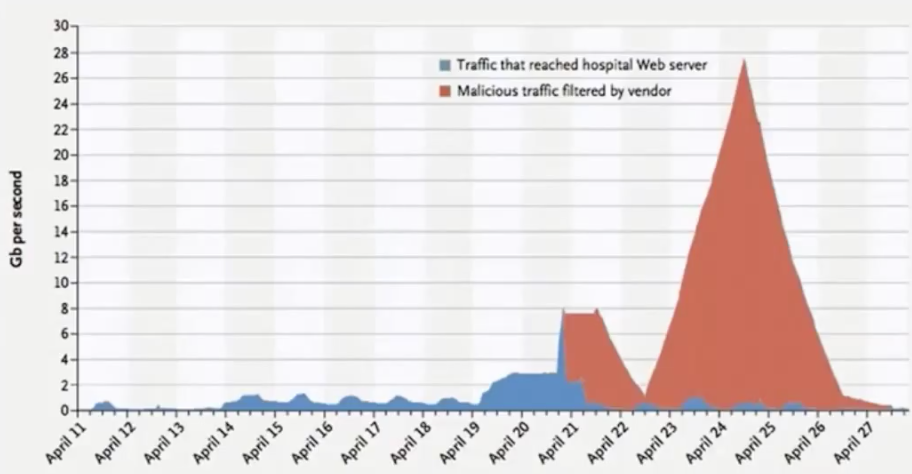
A graph of the bandwidth used in DDOS attack. The blue indicates what hit the hospital’s network. The red indicates what Radware was able to absorb.
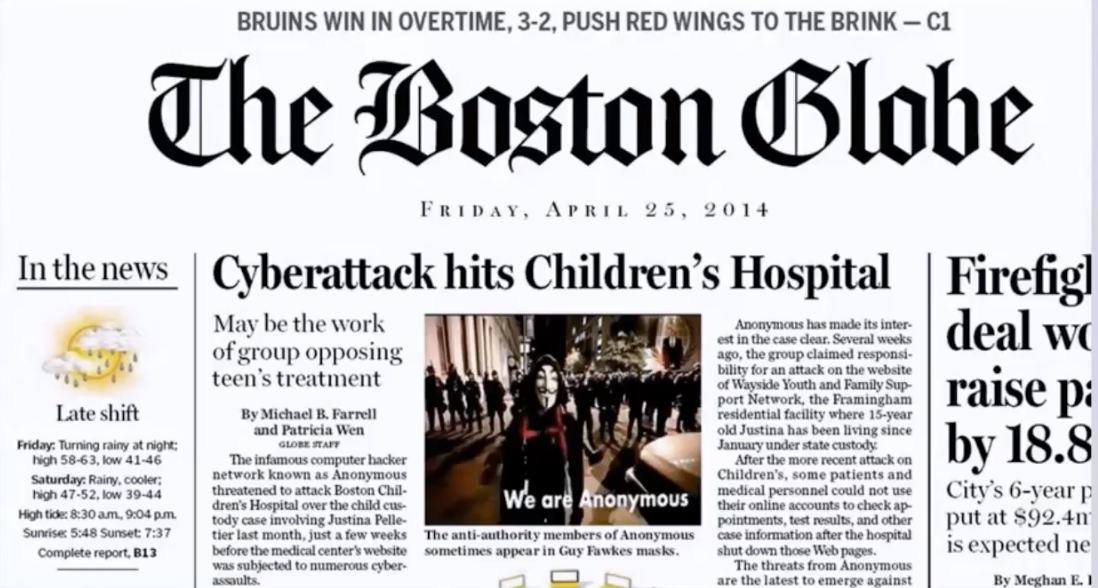
The Boston Globe newspaper ran a front page story about the attack.
Protesters gathered in support to free Justina.

A more popular anonymous account sent a tweet.
To all the "Anons" attacking the CHILDREN'S HOSPITAL in the name of Anonymous via Op #JustinaPelletier - IT IS A HOSPITAL: STOP IT.
— Anonymous (@YourAnonNews) April 25, 2014
References
The CIO of the hospital published a full report of this attack in the New England Journal of Medicine (paywall). http://www.nejm.org/doi/full/10.1056/NEJMp1407326
YouTube videos:
- Interview with Lou
- Interview with Justina
- Press conference in CT
- Justina returns home
- Protestors
- Hospital CIO presenting details of attack
Information about the hacker arrested:
- https://www.huffingtonpost.com/entry/why-i-knocked-boston-childrens-hospital-off-the-internet-a-statement-from-martin-gottesfeld_us_57df4995e4b08cb140966cd3
- https://www.dailywire.com/news/27155/still-jail-after-trying-save-young-girls-life-frank-camp
- https://www.freemartyg.com/
- https://www.scribd.com/doc/299575089/Gottesfeld-Martin-Affidavit-docx
Music
Music in this episode: “The Loss of Blood” and “Blood Loss” by Ian Alex Mac.
“Monkeys Spinning Monkeys”, “Ghostpocalypse - 5 Apotheosis”, “Unnatural Situation”, “Decisions”, and “Wisps of Whorles” by Kevin MacLeod Licensed under Creative Commons: By Attribution 3.0 License.
“Fibonacci”, “Books”, and “Flood” by Jahzaar.
Transcript
[FULL TRANSCRIPT]
JACK: Anonymous and activism often cross paths. When there are injustices in the world that triggers protests or riots there’s often online versions of those protests too, and if somebody wants to simply be the voice of the citizens of the world, they can be anonymous and make threats to an organization. These anonymous online protestors have targeted governments, churches, organizations, to try to expose their corruption. They have been known to wage online attacks so hard that the organization goes completely offline, or they take it a step further and get internal access to the network and cause whatever destruction they can from within.